Today is a good day for visitors to 1024kb.co.nz with the release of a new & improved updated Laptop BIOS Password Generator.
Now capable of providing BIOS Master Passwords for late model Dell XPS, Precision & Latitude laptops with -BF97 suffix BIOS ID, also improved -1F66 calculations too. Yup, the 1024kb.co.nz Laptop BIOS Master Password Generator now does even more late model laptops – for free. More requests come in for a solution Dell’s -BF97 BIOS than any other BIOS. To all those who asked – this one’s for you.

There’s various other improvements too – the Fujitsu Siemens 6×4 unlocker has been added to the Laptop BIOS Master Password Generator, so there’s no need to download Python any more.
This new, improved Laptop BIOS Password Generator @ 1024kb.co.nz means that if you have a recent Dell laptop with a lost/forgotten BIOS password, you now have a choice. You can pay up to $100 on other sites then wait nervously for your code to turn up in a few hours, or you can get it here – free & immediate. I know which way I’d go.
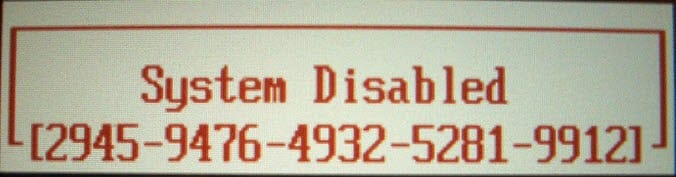
So yeah, boot it on over to the new, improved Laptop BIOS Master Password Generator @ 1024kb.co.nz, & get busy unlocking!